The term “DH58GOH9.7 code” may appear technical and confusing at first glance, but it is increasingly relevant in modern IT environments, including Egypt’s rapidly evolving digital landscape. Rather than being a traditional programming code, DH58GOH9.7 is typically a software identifier, firmware version label, or internal system reference used by developers and enterprises to manage complex systems.
In Egypt, where digital transformation is accelerating across industries such as banking, education, and government services, such backend identifiers play an important role in maintaining system efficiency, tracking updates, and ensuring secure operations. Understanding DH58GOH9.7 helps businesses and IT professionals better manage infrastructure and improve performance.
What is DH58GOH9.7 Code?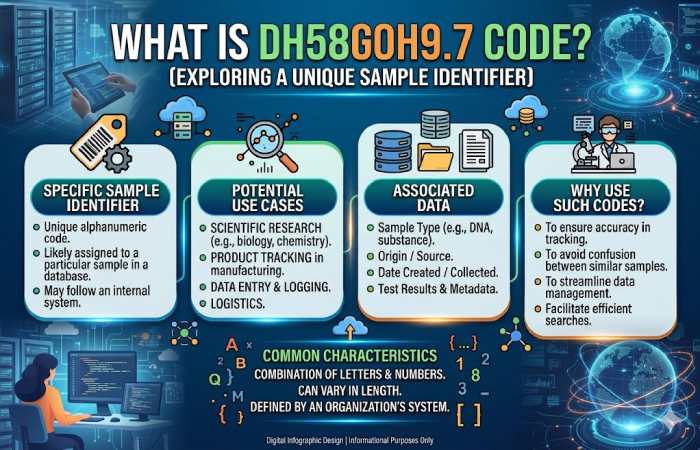
DH58GOH9.7 is best described as a technical naming structure used in software or hardware systems. It is not something users directly interact with, but rather a backend label that helps developers organize, track, and update systems.
The structure of the code can be broken down into meaningful parts:
| Component | Explanation |
| DH58 | Likely refers to a hardware or chipset series |
| GOH9 | Internal module or system identifier |
| .7 | Version number indicating updates or patches |
This type of naming is common in enterprise environments where systems need precise tracking and version control.
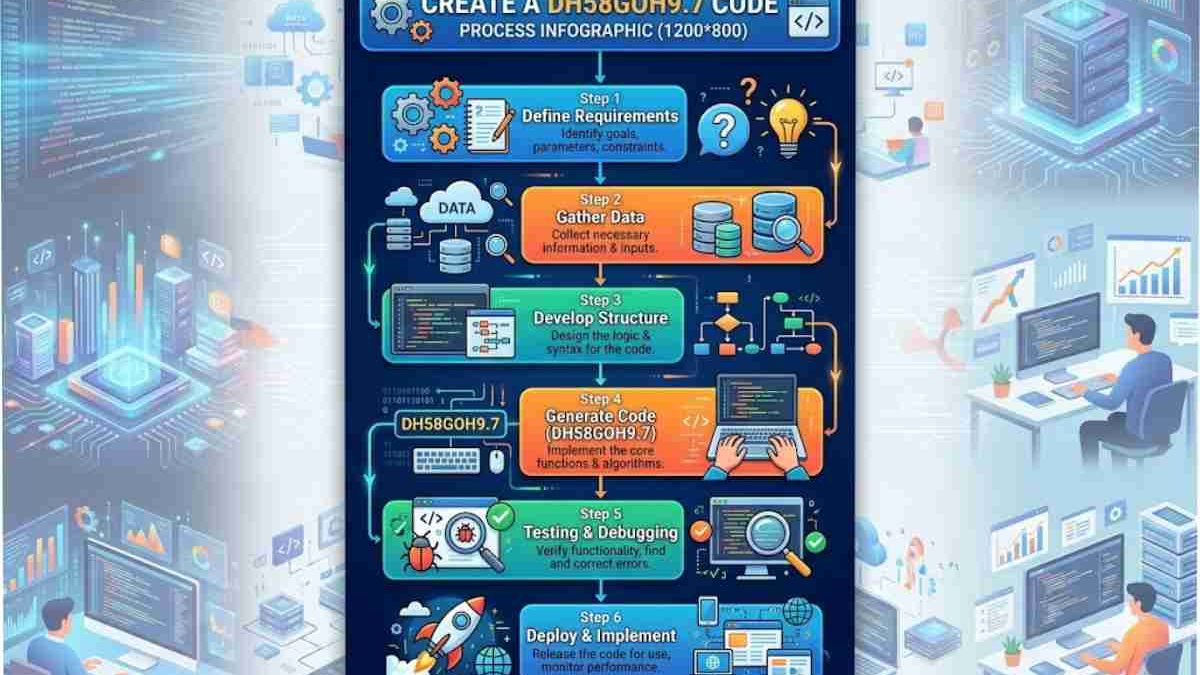
How DH58GOH9.7 Works in Practice
In real-world applications, DH58GOH9.7 functions as a reference point within a system. It may be used in firmware updates, software builds, or automation tools to identify a specific configuration or version.
Instead of being visible to everyday users, it operates behind the scenes, helping IT teams manage systems more efficiently. For example, when a company updates its infrastructure, codes like DH58GOH9.7 help ensure the correct version is deployed.
Key Features and Capabilities
Although DH58GOH9.7 is not a standalone product, systems associated with it often include advanced capabilities that align with modern enterprise technology trends.
| Feature | Description |
| Automation | Reduces manual work by automating repetitive tasks |
| Cloud Compatibility | Integrates with cloud-based platforms |
| Data Processing | Handles large volumes of data efficiently |
| Multi-platform Support | Works across various operating systems |
| Security Controls | Includes encryption and access management |
These features make such systems highly valuable in professional environments where efficiency and scalability are critical.
Importance of DH58GOH9.7 in Egypt
Egypt is experiencing significant growth in its digital economy, driven by government initiatives and private sector innovation. Technologies like DH58GOH9.7 are important because they support the backend infrastructure of modern systems.
Organizations in Egypt rely on such tools to streamline operations, improve service delivery, and maintain competitive advantages in a digital-first world.
Key Sectors Benefiting in Egypt
| Sector | Application |
| Banking | Secure transaction systems and automation |
| Government | Digital services and workflow management |
| Education | Online learning platforms |
| Startups | Data analytics and business automation |
| Telecom | Network and infrastructure management |
These use cases highlight how backend systems contribute to national digital growth.
Common Use Cases
DH58GOH9.7-type systems are widely used in enterprise environments for multiple purposes. One major use case is automation, where repetitive tasks are handled automatically, saving time and reducing human error. Another important application is in DevOps, where developers use such identifiers to track builds and manage software updates efficiently.
Additionally, DH58GOH9.7 may be linked to firmware or hardware systems, helping control device performance and ensuring compatibility between components. It is also relevant in data analytics platforms, where large datasets are processed to generate insights.
Benefits of DH58GOH9.7 Code
The use of structured system identifiers like DH58GOH9.7 provides several advantages for organizations, especially those operating in complex IT environments.
| Benefit | Explanation |
| Improved Efficiency | Automates workflows and reduces manual effort |
| Scalability | Supports business growth and system expansion |
| Enhanced Security | Protects data with advanced security layers |
| Flexibility | Adapts to various industries and use cases |
| Integration | Easily connects with APIs and external systems |
These benefits make it a valuable component of modern enterprise systems.
Challenges and Limitations
Despite its advantages, DH58GOH9.7 also comes with certain challenges. One of the main issues is the lack of public documentation, which can make it difficult for beginners to understand. Additionally, such systems often require technical expertise, creating a learning curve for new users.
Compatibility issues may arise when integrating with older systems, and there may be concerns about security if the code appears in unfamiliar contexts.
| Challenge | Details |
| Limited Documentation | Not widely explained publicly |
| Technical Complexity | Requires IT knowledge |
| Compatibility Issues | May not support legacy systems |
| Security Concerns | Unknown codes may raise risks |
| Limited Support | Fewer official support channels |
Is DH58GOH9.7 Safe?
The safety of DH58GOH9.7 depends largely on where it appears and how it is used. In most cases, it is safe when it originates from trusted software or system processes. However, if it appears unexpectedly, it should be investigated.
Organizations should follow best practices such as verifying sources, scanning systems for threats, and consulting IT professionals when necessary.
How to Identify DH58GOH9.7 in Your System
If you encounter DH58GOH9.7 in your system, it is important to identify its source and purpose. This process involves checking system logs, reviewing installed software, and running security scans.
| Step | Action |
| 1 | Check system logs |
| 2 | Identify associated software |
| 3 | Search for documentation |
| 4 | Run antivirus scans |
| 5 | Contact IT support if needed |
Taking these steps ensures that the code is legitimate and not a security risk.
Comparison with Traditional Software
DH58GOH9.7 differs significantly from traditional software applications. While most software is designed for direct user interaction, this type of code operates in the background.
| Feature | DH58GOH9.7 | Traditional Software |
| Visibility | Backend only | User-facing |
| Naming Style | Technical | Brand-based |
| Usage | System-level | Application-level |
| Accessibility | Limited | Public |
| Documentation | Minimal | Extensive |
This comparison helps clarify its role within the IT ecosystem.
Future Outlook in Egypt
As Egypt continues to invest in digital infrastructure, the importance of backend systems like DH58GOH9.7 is expected to grow. Emerging technologies such as artificial intelligence, cloud computing, and smart city initiatives will rely heavily on such systems.
In the future, DH58GOH9.7-like frameworks may evolve into more advanced platforms, offering greater automation, improved security, and easier integration. This will further support Egypt’s vision of becoming a leading digital economy in the region..
Final Thoughts
The DH58GOH9.7 code represents a critical part of modern IT systems, even though it operates behind the scenes. It is not a traditional code but a technical identifier used for managing software, firmware, and enterprise systems.
In Egypt, where digital transformation is rapidly progressing, such systems are essential for improving efficiency, ensuring security, and supporting innovation. By understanding DH58GOH9.7, businesses and professionals can better navigate the complexities of modern technology and make informed decisions.
